
A recent study found that the global cloud services market is valued at $454 billion and is expected to surpass $2 trillion by 2032. As businesses continue to shift toward cloud integration, security becomes more and more urgent. Even though the Cloud is much more secure than traditional on-premises data centers, vulnerabilities still exist. These vulnerabilities make investing in cloud security services vital.
What exactly is cloud security? Cloud security is a set of tools, frameworks, and protocols to protect data (in motion and at rest) from unauthorized access, theft, or malware threats. Cloud security spans assorted technologies to defend public, private, and multi-cloud environments, whether Infrastructure as a Service (IaaS), Software as a Service (SaaS), or Platform as a Service (PaaS).
When configured correctly, cloud-integrated security keeps organizations profitable by defending against the negative ramifications of a data breach, such as losses in paid ransom, reputational damage, regulatory action such as fines or license suspension, as well as guarding end-user data. Like other elements of cloud computing, your security team becomes cost-efficient by switching from the capital expense model to operating expenses. Bills come from small, monthly subscriptions and service fees instead of costly, upfront investments.
If cloud computing is more secure than on-prem, why worry about it? Gartner calculated that organizations lose an average of $5,600 per minute of downtime experienced from a malware attack. Besides shrinking your attack surface and lowering the likelihood of a breach, cloud security can help maintain business continuity in the event of a successful breach or natural disaster. Data protection services such as managed backup and Disaster Recovery as a Service (DRaaS) ensure minimal downtime and maintain data compliance.
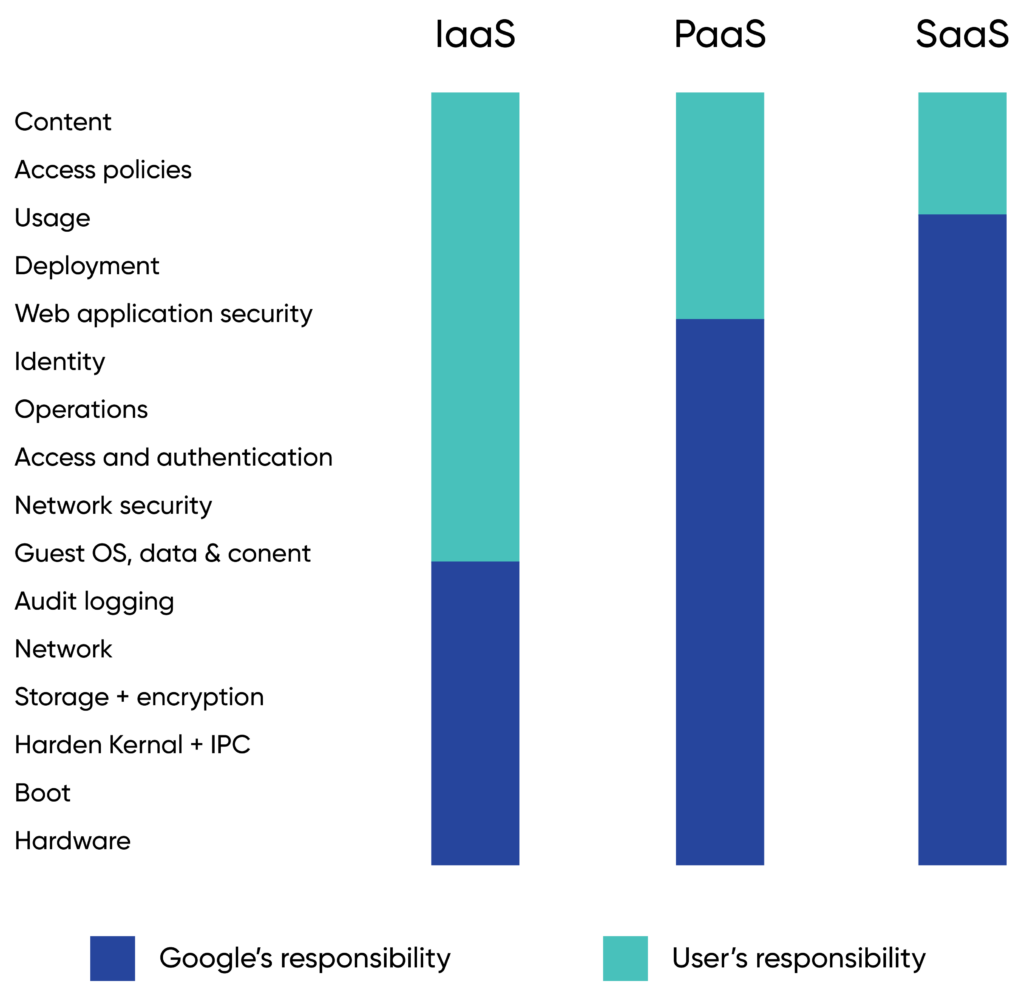
Cloud security utilizes the shared responsibility model, in which a cloud service provider (CSP) and the customer share the burden of defending cloud systems. Confusion sometimes arises about who exactly is responsible for what.
There are minor differences between each CSP and which model of cloud you choose: IaaS, PaaS, SaaS, or some combination of all three.
Generally, the cloud service provider is responsible for the security of:
The customer is responsible for securing the following:
Note that network security is the customer’s responsibility in IaaS.
Unlike the digital security models of the past, the Cloud does not have a defined perimeter. The castle-and-moat model, in which a firewall is established around a data center, is ineffective for the Cloud because each point of presence (PoP), application, and network represents potential weak points.
Other challenges to cloud security include:
Known as the CIA triad, cloud data security follows the same guidelines as information security:
A data breach violates one or more of these tenets. The CIA triad is a valuable tool security professionals utilize in organizational risk assessment. Additionally, the NIST has created another assessment tool, the Five Pillars of Cybersecurity. They include:
At CBTS, we build on this assessment tool and define our own six pillars of cloud security:
Learn more: The six pillars of cloud security
Yet another framework that guides cloud security is zero trust. The concept of zero trust in cloud security was introduced in 2010 by Forrester. It emphasizes not trusting anyone or anything within or outside the network. Instead, everything needs to be authorized, inspected, and secured. Zero trust promotes a least privileged governance strategy and requires developers to fortify web-facing applications properly. Micro-segmentation is also used to create secure zones and traffic between them.
No single technology or solution fully encompasses integrated cloud security. The key is appropriately implementing and integrating cloud security tools and creating greater efficiencies between them for the most robust security posture possible. Even with the enhanced security offered by CSPs, your organization needs to fully understand where it’s protected in service-level agreements (SLAs) and where potential vulnerabilities lie. The best way to do so is to partner with an experienced cloud security vendor.
With years of experience managing enterprise data centers on-prem and in the Cloud, CBTS delivers the latest technologies in managed cloud security services and backup solutions. Our team maintains relationships with top CSPs and security providers to offer comprehensive protection against cyberattacks and downtime. At CBTS, we strive to understand your unique business challenges and provide the necessary expertise, training, and certifications to protect your business from data breaches, theft, and other common causes of system outages.