When talking about information privacy, some people think it’s the same thing as information security, but for security professionals, they are not the same thing.
If you talk about privacy, you are really talking about confidentiality.
When talking about keeping information —or data—secure, information security professionals focus on three key things: Confidentiality, integrity, and availability, also known as the CIA triad, which is the foundation of any organization’s security program. If you think about it visually, it would look like this:
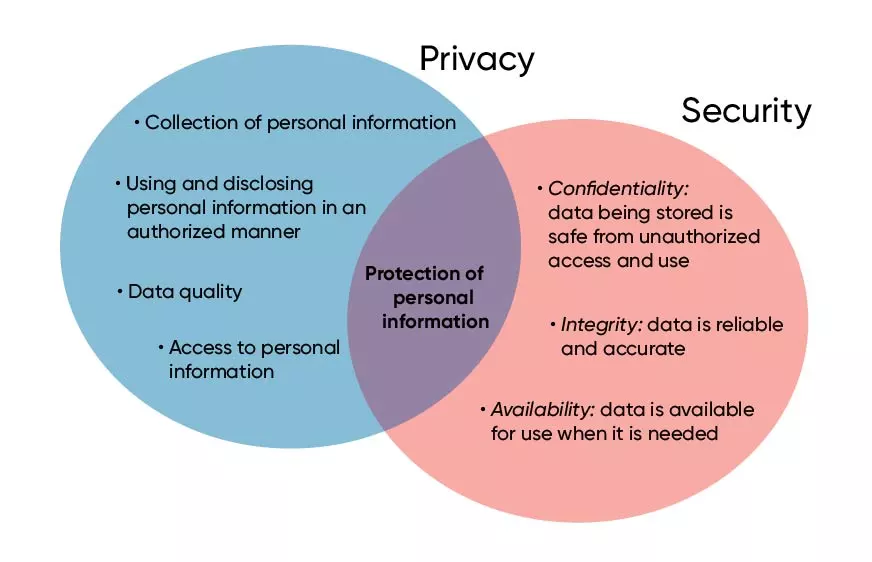
Privacy focuses on how personal data is used and controlled. The graphic puts privacy in that circle of how companies collect personal information, how they use that personal information in an authorized manner, and how they ensure the information is accurate.
Security focuses on keeping the data safe from unauthorized access and use, making sure the data reliable and accurate, and ensuring the data is available for use when needed.
Let’s look at examples to show the difference between privacy information and security
We’ll start with Amazon, an entity that touches almost everyone’s information in some way, shape, or form.
Amazon and privacy
If you buy products online from a vendor like Amazon, you expect that they will keep the information you share with them confidential. This information includes things like where you live (shipping information), how you are paying for your purchases (credit card or debit card), what you buy (shampoo, jewelry, clothing, personal items), and how often you buy things (once a week, once a month, etc.). All this information that Amazon has stored about you is related to information (data) that you would most likely want to keep private.
Note that none of your order information is personally identifiable information (PII), except for your method of payment.
In this example, you shared personal information with Amazon with certain expectations: For starters that Amazon will keep that information private and not disclose it to just anyone; and secondly, that only authorized people at Amazon can see your personal information.
Despite all the questions this suggests, today we won’t go into how Amazon makes money from selling your information to various companies. The terms of use of your information is in the privacy terms between you and Amazon.
Amazon and security
From Amazon’s the point of view, the focus is the CIA triad and ensuring that:
1. The information they are storing about you stays confidential (e.g., it’s not stolen by a competitor or criminal gang).
2. This data maintains its integrity, that is, it is not changed in some way by someone (e.g., your order is changed from 1 pair of socks to 10, or the price is changed from $10 to $1); and
3. The data is available, so that you can see your order anytime, day or night, from anywhere on any device.
Equally important to Amazon is that this data is available to them when they want it so they can pick the right quantities, ship it to the right address, charge the right credit card, etc.
In this example, Amazon keeps the information you share confidential and available, and at the same time ensures that it hasn’t been modified and has maintained its integrity. For more on privacy, review how SD-WAN answers the challenge of remote workforce networking.
How do financial institutions treat information privacy and security?
As a consumer, one of your primary concerns is the trustworthiness of the business that takes care of your hard-earned money.
Your bank and privacy
Your bank or credit union has a lot of sensitive information about you, much of which is personally identifiable information, or PII. They know your name, address, age, social security number, and bank account numbers; the balances of your credit card, mortgage, savings and checking accounts; and the amount of your paycheck and how frequently you are paid. You most definitely want this data to remain private and confidential.
Not surprisingly, your bank also wants to keep your information private, particularly according to Federal regulations regarding PII and PCI (credit card). At the same time, your bank wants you to feel like you can trust them with this very private, very personal information.
Incidentally, banks also sell your information based on the privacy agreements that you agreed to when you opened the account, but this is a topic we also won’t address in this blog post.
Read up on how CBTS UCaaS services are PCI compliant.
Your bank and security
Banks also want to keep your information secure, and also follow the CIA triad. They make sure your information is kept confidential, so that only the appropriate people can see your PII and other bank-specific information.
To prevent your account balances from being not manipulated in some way, the integrity and accuracy of your account information is essential to your bank or credit union. Your bank also makes your account information (your data) available so that you can check your balances and access your money any time, from anywhere. Like Amazon, the bank works to keep your information confidential and available and maintains the integrity of the data so that it is used appropriately and according to the privacy terms you agree to when you opened the account (see the privacy terms for US Bank).
Are you all clear on information privacy and security now?
Hopefully these examples help clarify the difference between privacy—keeping your sensitive data private—and security—which ensures that your data is kept confidential and available in a way that maintains its integrity.
If you want to limit what any business—like Amazon or your bank—knows about you, find and review the data sharing policies with the companies you use. Also, some companies provide options for limiting how your personal information is shared with other companies. Those details are in the company privacy policies which you can typically and easily find online. Security doesn’t just happen. Learn why you should do information security awareness and training.